Core Security. Balancing Internal and External Pen Testing
With the threat landscape expanding and criminals taking advantage of security gaps, organizations are turning to controls that can help them limit their exposure. Among other controls, penetration testing stands out because it simulates attackers’ malicious activities and tactics to identify security gaps in business systems or applications. A penetration test aims to understand what vulnerabilities are in business systems, how they could be exploited, and the potential impact if an attacker were successful. Because pen tests thoroughly investigate vulnerabilities, the scope of each pen test must be limited and may differ from test to test. Pen tests take on two different types of perspectives: internal and external. In this blog, we will examine what internal and external penetration testing is, who conducts these tests, and why organizations need both.
Getting Past the Perimeter: External Pen Testing
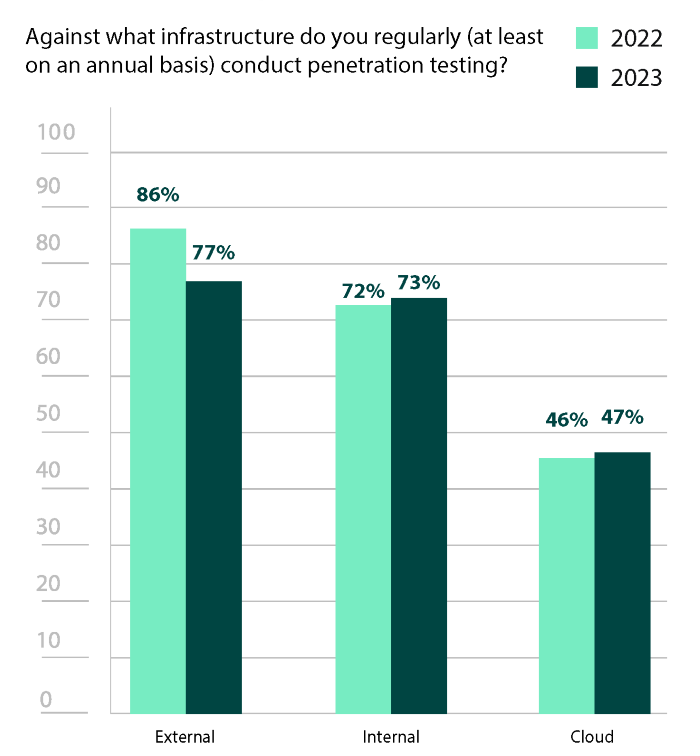
The 2023 Pen Testing Report revealed that 77% of security professionals pen test their external infrastructure. Essentially, external networks encompass all public-facing assets—including the internet at large. Additionally, many organizational applications, like mail servers, websites, or even customer portals maintain a connection to these external networks and can also provide a doorway from which a threat actor can pivot.
External penetration tests are typically what people think of when they hear about pen testing. These tests use the same techniques as adversaries to attempt to exploit weaknesses in an organization’s front facing perimeter or attempt to bypass them altogether with strategies like a phishing campaign or other social engineering methods.
Thinking Beyond the Initial Breach: Internal Penetration Testing
This year’s report also showed that 73% of security professionals pen test their external infrastructure. Internal penetration tests take on the role of an adversary who has already gained a foothold within the corporate network and is looking to elevate privileges to move laterally, gain further control and cause more damage. These assumed breach scenarios also deal with security gaps that such an attacker could exploit.
Internal attacks can originate from malicious insiders or compromised users like careless employees, insecure third-party vendors, and even clients or customers. Internal threats can be anything from bad hygiene habits, like weak passwords and poor access controls, to system and app misconfigurations and insecure endpoints. The Verizon 2022 Data Breach Investigations Report indicates that human errors are responsible for 13% of data breaches.
Though many think pen tests concentrate on an initial breach, it’s just as important to deploy tests that focus on what happens once someone is already inside the perimeter. Since such attacks start with internal access, they may attempt to achieve more high-value objectives including acquiring high-level privileges, compromising the Domain, or accessing other valuable assets and/or information. Because of this, it is crucial to identify and prioritize these threat vectors.
Who Should Be Conducting These Pen Tests?
Though it’s easy to think that in-house teams would handle all internal tests and external/third party teams would handle external tests, this is not the case. Both teams can conduct internal and external pen tests.
The one exception may be physical pen tests. These external tests involve attempting to gain entry to a physical facility, system, or network by exploiting weaknesses like doors, locks, cameras, or other access controls. Third parties tend to be the only teams that complete such assessments. 36% of respondents to the pen test report used third-parties for such services.
Otherwise, using both types of teams simply provides the capability to conduct more tests. Internal teams can conduct routine tests more often, while third-party services are solicited to provide a fresh prospective and different skill sets.
Creating a Holistic Pen Testing Strategy
Though organizations have to make tough choices when deciding what tests they have the time and resources to run, one of the most important criteria to consider is whether you’re balancing internal and external tests.
Only testing externally overlooks vulnerabilities that can be exploited by a malicious insider or a compromised account. With strategies like phishing more popular than ever, it’s critical to remember how easily insider access can be attained. However, only testing internally can inadvertently leave a door wide open for an attacker to get in without much difficulty.
Ultimately, by conducting both internal and external pen testing, organizations can gain full visibility into their security posture and ensure that they are adequately protected. The pen test report showed that in 2022, internal environments were regularly tested 14% less than external environments. With a gap of only 4% in 2023, it’s encouraging that this year’s pen testing report show that organizations are better understanding this balance.
Source: Core Security

