Sophos Central Architect Training (11-13 February 2020)
This course provides an in-depth study of Sophos Central, designed for experienced technical professionals who will be planning, installing, configuring and supporting deployments in production environments. It consists of presentations and practical lab exercises to reinforce the taught content, and electronic copies of the supporting documents for the course will be provided to each trainee through the online portal. The course is expected to take 3 days to complete, of which approximately 9 hours will be spent on the practical exercises.
Requirement
Prior to attending this course, trainees should:
- Complete the Sophos Central Endpoint and Server Protection and should have passed the Certified Engineer exam
- Experience with Windows networking and the ability to troubleshoot issues
- A good understanding of IT security
- Experience using the Linux command line for common tasks
- Experience configuring Active Directory Group Policies
- Experience creating and managing virtual servers or desktop
Target audience:
This course is designed for technical professionals who will be planning, installing, configuring and supporting deployments in production environments. And for individuals wishing to obtain the Sophos Central Certified Architect certification.
Objectives:
On completion of this course, trainees will be able to:
- Design an installation considering all variables
- Undertake a multi-site installation appropriate for a customer environment
- Explain the function of core components, how they work, and how to configure them
- Track the source of infections and cleanup infected devices
- Perform preliminary troubleshooting and basic support of customer environments
Certification:
To become a Sophos Certified Architect, trainees must take and pass an online assessment. The assessment tests their knowledge of both the presented and practical content. The pass mark for the assessment is 80%, and is limited to 3 attempts.
Duration: 3 days
Content
- Module 1: Deployment Scenarios (60 mins)
- Module 2:Client Deployment Methods (65 mins)
- Module 3:Endpoint Protection Policies (80 mins)
- Module 4:Server Protection Policies (30 mins)
- Module 5:Protecting Virtual Servers (60 mins)
- Module 6:Logging and Reporting (45 mins)
- Module 7: Managing Infections (45 mins)
- Module 8: Endpoint Detection and Response (30mins)
- Module 9:Management (65 mins)
Course content
Module 1: Deployment Scenarios (60 mins)
-
- Identify some of the common challenges when deploying Central
- Deploy Update Caches – Set up Message Relays
- Configure AD Sync Utility
- Identify where Update Caches and Message Relays should be used
- Labs (45 mins)
- Register and activate a Sophos Central evaluation
- Install Server Protection
- Install and Configure AD Sync Utility
- Deploy an Update Cache and Message Relay
Module 2: Client Deployment Methods (65-75 mins)
- Identify the recommended steps for deploying Sophos Central
- Explain the installation process, and identify the different types of installer
- Automate deployment for Windows, Linux and Mac computers
- Migrate endpoints from Enterprise Console
- Locate installation log files
- Remove third-party products as part of a deployment
- Labs (75-90 mins)
- Enable Server Lockdown
- Deploy using Active Directory Group Policy
- Use the Competitor Removal Tool
- Deploy to a Linux Server using a Script
Module 3: Endpoint Protection Policies (80-90 mins)
- Describe the function and operation of each of the components that make up an Endpoint Protection and Intercept X
- Configure policies to meet a customer’s requirements and follow best practice
- Test and validate Endpoint Protection
- Configure exclusions
- Configure Data Loss Prevention
- Labs (100-120 mins)
- Test Threat Protection Policies
- Configure and Test Exclusions
- Configure Web Control Policies
- Configure Application Control Policies
- Data Control Policies
- Configure and test Tamper Protection
Module 4: Server Protection Policies (30 mins)
- Configure Server Protection Policies
- Configure and Manage Server Lockdown
- Labs (65-75 mins)
- Configure Sever Groups and Policies
- Manage Server Lockdown
- Test Linux Server Protection
Module 5: Protecting Virtual Servers (60 mins)
- Connect AWS and Azure accounts to Sophos Central – Deploy Server Protection to AWS and Azure
- Deploy and Manage Sophos for Virtual Environments
- Labs (60 mins)
- Download the installer for the Security Virtual Machine
- Install the Security Virtual Machine (SVM) on a Hyper-V Server
- Configure Threat Protection policies to apply to the Security VMs and the Guest VMs they protect
- Perform a manual installation of the Guest VM Agent and view logs
- Test and configure a script to deploy the GVM Agent
- Manage Guest VMs from the Central Console
- Test Guest VM Migration
Module 6: Logging and Reporting (45 mins)
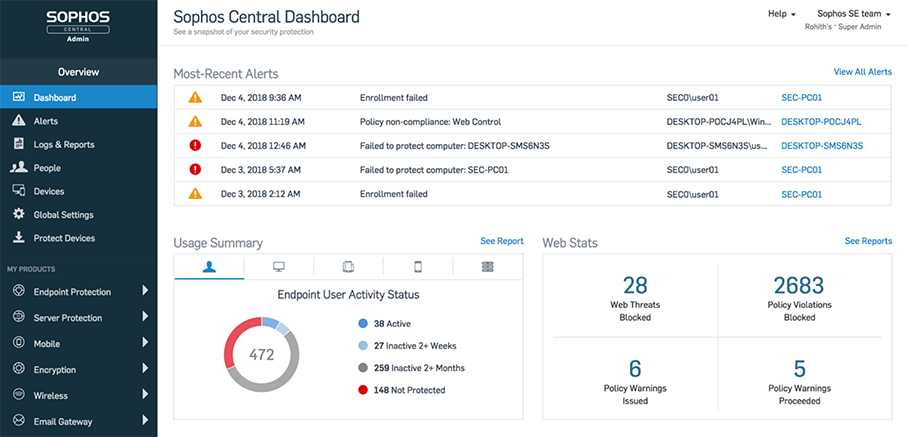
- Explain the types of alert in Sophos Central, and be able to read an RCA
- Use the Sophos Central logs and reports to check the health of your estate
- Export data from Sophos Central into a SIEM application
- Locate client log files on Windows, Mac OS X and Linux
- Labs (55-60 mins)
- Generate and analyze an RCA
- Configure SIEM with Splunk
Module 7: Managing Infections (45-60 mins)
- Identify the types of detection and their properties
- Explain how computers might become infected
- Identify and use the tools available to cleanup malware
- Explain how the quarantine works and manage quarantined items
- Cleanup malware on a Linux Server
- Labs (40 mins)
- Source of Infection Tool
- Release a File from SafeStore
- Disinfect a Linux Server
Module 8: Endpoint Detection and Response (30 mins)
- Explain what EDR is and how it works
- Demonstrate how to use threat cases and run threat searches
- Explain how to use endpoint isolation for admin initiated and automatic isolation
- Demonstrate how to create a forensic snapshot and interrogate the database
- Labs (30 mins)
-
- Create a forensic snapshot and interrogate the database
- Run a threat search and generate a threat case
Module 9: Management (65 mins)
- Use the Controlled Updates policies appropriately
- Enable multi-factor authentication
- Use the Enterprise Dashboard to manage multiple sub-estates
- Identify the benefits of the Partner Dashboard
- Identify common licensing requirements
- Labs (25 mins)
- Enable Manually Controlled Updates
- Enable Multi-Factor Authentication
Agenda
Trainer: Michael Eleftheroglou
Day 1 Tuesday 11 February 2020
9:30-10:30 Deployment Scenarios
10:30-10:45 Break
10:45-11:30 Labs
11:30-11:45 Break
11:45-13:00 Client Deployment Methods I
13:00-14:00 Break Lunch
14:00-15:30 Labs
15:30-15:45 Break
15:45-17:15 End Point Policies
Day 2 Wednesday 12 February 2020
9:30-11:15 Labs
11:15-11:30 Break
11:30-12:00 Server Protection Policies
12:00-12:15 Break
12:15-13:30 Labs
13:30-14:30 Break- Lunch
14:30-15:30 Protecting Virtual servers
15:30-15:45 Break
15:45-16:45 Labs
16:45-17:30 Logging and Reporting
Day 3 Thursday 13 February 2020
9:30-10:30 Labs
10:30-10:45 Break
10:45- 11:30 Managing Infections
11:30-12:00 Labs
12:00-12:10 Break
12:10-12:40 Endpoint Detection and Response
12:40-13:45 Management
13:45-14:45 Break – Lunch
14:45-17-15 Labs and Exams